Bringing Ludicrous Mode to the Data Center the Easy Way
By: Western Digital View more from Western Digital >>
Download this next:
5G vs. Wi-Fi 6: What's the difference?
By: TechTarget ComputerWeekly.com
Type: Infographic
As organizations move out of crisis mode, CIOs are rethinking their digital transformation strategies. So what's on the minds of IT and business leaders that will drive digital transformation trends in 2022? Here are five key areas CIOs are focusing on as we move out of crisis mode and into the future, with Intelligent search, CDPs, AIOps, DevOps/Agile/ITSM claiming the spotlight.
These are also closely related to: "Bringing Ludicrous Mode to the Data Center the Easy Way"
-
Infographic: 2019 Europe IT Priorities - Business Applications
By: TechTarget ComputerWeekly.com
Type: eGuide
In this infographic, we take a look at what the most popular business applications being deployed, the most popular deployment models and the most popular applications being deployed in SaaS mode. Survey results taken from the 2019 IT Priorities survey carried out by ComputerWeekly.com, ComputerWeekly.de and LeMagIT.fr.
-
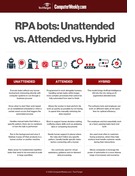
RPA bots compared: Unattended vs. Attended vs. Hybrid
By: TechTarget ComputerWeekly.com
Type: Infographic
Robotic process automation (RPA) is a hot commodity in today's enterprises. In just about every industry, executives are turning to automation to increase efficiencies, reduce human errors, improve customer experience and cut costs, with many of them opting for RPA to do the job.
Described as transformational and disruptive, RPA bots can be divided into three modes -- unattended, attended and hybrid -- depending on how they operate within the enterprise. In this infographic, we compare the main similarities and differences between the three modes and examine how organizations can benefit from each of them.
Find more content like what you just read:
-
Application Delivery Network Buyers' Guide
By: TechTarget ComputerWeekly.com
Type: eGuide
The more systems become remote, the less secure they are. On face value a huge cliché – or truism - but sadly actually true. And sadly, for those running networks, something that is going to be truer – or more clichéd – as remote working continues to proliferate in the new normal of the hybrid mode of working.
-
Green initiatives are delivering disappointing ROIs for today's data centers
By: TechTarget Data Center
Type: eBook
In the following expert handbook, readers will learn about several ways they can help reduce the cost of power consumption in the data center, effecting greater energy efficiency.
-
Financial maturity roadmap: 4 steps for success
By: Citrin
Type: White Paper
Today, manufacturing and distribution companies face more pressure than ever to improve efficiency and reduce costs while still getting superior products to market quickly. However, poor technology can be the reason you don’t achieve your goals. Browse this guide to learn more.
-
3 things to consider when moving your data to the cloud
By: AllCloud
Type: Blog
While many tout the benefits of the cloud such as scalability and cost savings, no one ever promotes the cloud as being easy. Whether your cloud data and analytics platform is on-prem or moving to the cloud, you need the same attention to strategy, process, and testing. While that may sound easy, those in IT know better. Read on to learn more.
-
Browser isolation: Your key to combatting cybercrime
By: Cradlepoint
Type: White Paper
Despite the ease and sophistication that browsers have brought to internet use, they also have become the target choice for cybercriminals looking to hack into your organization and personal data. But why exactly is this? Dig into this white paper to learn more.
-
Audio for Effective Collaboration in a Hybrid World: 4 Ways to Make It Happen
By: Shure Inc
Type: Resource
Tap into this Frost & Sullivan visual and interactive white paper to uncover 4 practical steps to leverage audio as a foundational tool for employee engagement and success—empowering everyone to hear and communicate effectively.
-
The Complete Guide to Outsourcing Finance
By: Citrin
Type: White Paper
Today, manufacturing & distribution companies need better decision-support capabilities to grow. At the same time, it's increasingly hard for smaller companies to find and retain the talent needed to advance their finance function—making it feel impossible to get out of reaction mode.
-
Jargon Buster Guide to Unified Communications
By: TechTarget ComputerWeekly.com
Type: eGuide
In this e-guide we will explore and define some of the key elements of a UC deployment and offer some insight into some of the emerging trends that are changing the way we communicate in our working lives.
-
Mobile World Congress 2019: The year 5G use cases got real
By: TechTarget ComputerWeekly.com
Type: eGuide
In this e-guide we will examine some of the bigger themes that emerged over the course of Mobile World Congress 2019 - which now attracts over 100,000 people every year.
-
Threat prevention techniques: How to build a strong network
By: TechTarget Security
Type: eGuide
Consult this expert E-Guide to learn how you can develop best practices for threat management and how you can build a strong network. Find out tips from the experts on how you can build a foundation for complete threat protect ion by consulting this guide now.
-
Building a flexible data center: Prepare for future growth
By: TechTarget Data Center
Type: eGuide
This feature eGuide offers answers for all of the potential data center questions you may be having as you embark on your journey to build a flexible data center in this down economy. Download now and identify some of the required factors for your data center construction.
-
Information Security Essential Guide: The Evolution of Threat Detection and Management
By: TechTarget Security
Type: Essential Guide
This Information Security Essential Guide outlines the latest threat detection options available, provides a number of best practices for threat prevention, and outlines why your SIEM is a key player in the fight against cybercrime.
-
Computer Weekly 29 January 2019: A vintage digital transformation for Majestic Wines
By: TechTarget ComputerWeekly.com
Type: Ezine
In this week's Computer Weekly, we examine the digital transformation of retailer Majestic Wines and find out how buying rival Naked Wines led to a cloud overhaul of the firm's IT. We look at the challenges for IT managers as they prepare for the end of Windows 7 support. And our buyer's guide discusses deep learning technology. Read the issue now.
-
Serving up server hardware
By: TechTarget ComputerWeekly.com
Type: eGuide
In this e-guide, find out why some companies are still hanging on to older hardware, the pros and cons of different types of server hardware, and what one Chinese tech giant is doing in the microprocessor space.
-
Royal Holloway: Cloud-native honeypot deployment
By: TechTarget ComputerWeekly.com
Type: Research Content
Exploring open problems facing cloud infrastructure, this article in our Royal Holloway security series describes the implementation, feasibility and benefits of cloud-native honeypots.
-
Computer Weekly – 13 February 2018: On the path to diversity in tech
By: TechTarget ComputerWeekly.com
Type: Ezine
In this week's Computer Weekly, after the UK celebrated 100 years of women's suffrage, we look at what more needs to be done to encourage greater diversity in IT to help tackle the ongoing skills shortage. We examine how mobile app developers can improve security. And we look at the role of containers in storage architecture. Read the issue now.
-
CIO Trends #2: Nordics
By: TechTarget ComputerWeekly.com
Type: eGuide
Computer Weekly talks to more IT leaders than any other publication, and our reporters gather in-depth insights into the challenges facing CIOs, CTOs and CDOs. This guide offers a collection of our most popular articles for IT leaders,
-
CIO Trends #2
By: TechTarget ComputerWeekly.com
Type: eGuide
Computer Weekly talks to more IT leaders than any other publication, and our reporters gather in-depth insights into the challenges facing CIOs, CTOs and CDOs.
-
Definitive Guide to Exchange Server 2010 Migration: Chapter 1: Under the Hood of Exchange Server 2010
By: TechTarget Data Center
Type: eBook
Migrating to Exchange Server 2010 from the 2007 edition is becoming a must, as the 2010 edition offers improved email archiving, high-availability, and optimal storage features. But as you begin to explore the possibilities of upgrading to Exchange 2010, do you have a proper plan in place?
-
How to overcome the complexities of logistics services
By: Blue Yonder
Type: White Paper
When it comes to logistics and shipping, it’s a fact that transportation management is growing more complex by the day and has become even more essential to the success of many businesses. To ensure that the entire transportation lifecycle is optimized, you need a robust, cloud-based transportation management platform. Read on to learn more.
-
Adobe Acrobat with Document Cloud Services Security Overview
By: Adobe
Type: White Paper
This white paper describes the defense-in-depth approach and security procedures implemented by Adobe to bolster the security of Adobe Acrobat with Document Cloud services and associated data.
-
A Security Assessment of Android Full-disk Encryption
By: TechTarget ComputerWeekly.com
Type: eGuide
This article in our Royal Holloway Security Series describes an attack on Android 5.0 full disk encryption and discusses potential countermeasures.
-
Learn application security in a practical way
By: VMware Tanzu
Type: eBook
Application security is a hot topic in the digital-first era. Developers today face more cyber threats than ever before. Because of that, it is critical that all developers continue to enhance their skillset. For those developers who want to learn more about app security, but in a practical way, this eBook is what you need. Read on to learn more.
-
CIO Trends #2
By: TechTarget ComputerWeekly.com
Type: eGuide
Computer Weekly talks to more IT leaders than any other publication, and our reporters gather in-depth insights into the challenges facing CIOs, CTOs and CDOs.
-
Logi Bolt wireless technology at a glance
By: Logitech Inc.
Type: eBook
Download this e-book to gain access to best practices and recommendations for optimizing the performance of Logi Bolt wireless products in your workplace environment.
-
Software-Defined Networking Strategies for Campus WANs
By: Brocade
Type: eGuide
In this E-Guide from SearchNetworking.com, explore some of the issues associated with troubled OpenFlow switches, which vendors carry them, and details about a strategy that will not cause you the issues these other switches do.
-
CASB, CSPM, CWPP Emerge as Future of Cloud Security
By: Palo Alto Networks
Type: eGuide
In this eguide, learn about the emergence and the future of Cloud security tools that will help bring successful and securely protected cloud environments.
-
SIP contact centers: Key benefits and potential challenges
By: TechTarget Security
Type: eGuide
Learn how Session Initiation Protocol (SIP), unified communications (UC) and contact centers fit hand in hand in this e-guide from SearchUnifiedCommunications.com.
-
A Computer Weekly E-Guide on Wired and Wireless LAN
By: TechTarget ComputerWeekly.com
Type: eGuide
When looking the way in which the Covid-19 pandemic has changed business life, a number of key areas have come to the fore: SD WAN, SASE and in particular digital transformation are key examples of that. Yet very little of the discourse includes something that is still really at the heart of the vast majority of firms: The local area network (LAN).
-
Content Filtering: Taming the Wild Web
By: TechTarget Security
Type: eGuide
Despite the countless opportunities and benefits the Internet provides, it also introduces a number of business risks. In this e-guide, uncover expert advice on how to mitigate risks with content filtering as well as how to balance web control with employee privacy.
-
A Computer Weekly e-guide on Network Visibility, Performance and Monitoring
By: TechTarget ComputerWeekly.com
Type: eGuide
Traditional discourse around networks is centred around the basic premise of if you build it they will come. And if they come, they will be able to use the network to its fullest extent and everyone will be happy.
-
Reduce the risk of cyber incidents from wireless peripherals
By: Logitech Inc.
Type: White Paper
The risk of a cyber incident hitting your organization goes up every single year. Along with risks going up, the cost of a breach is also increasing just as fast. However, with so many attack vectors available, IT leaders need to be aware of all points of vulnerability in the business. This even includes wireless peripherals. Read on to learn more.
-
Free chapter: ITF+ CompTIA IT Fundamentals
By: McGraw Hill
Type: Book
Download this sample chapter from ITF+ CompTIA IT Fundamentals to learn how to approach IT problems using a standard troubleshooting method, how to troubleshoot common computer problems and more.
-
Mobile Payments Using Host Card Emulation with NFC
By: TechTarget ComputerWeekly.com
Type: Research Content
In this article from our Royal Holloway security series, we present a set of risks associated with using smartphones for contactless payment transactions.
-
Safeguard documents at every touchpoint
By: Adobe
Type: eBook
Dive into this eBook to discover how Adobe Document Cloud for enterprise mitigates risks across document lifecycles with a robust, multi-layered security approach. You’ll learn how these solutions help teams maximise their technology investment.
-
Expert guide to mobile unified communications: Implementation best practices
By: TechTarget Security
Type: eGuide
This expert e-guide uncovers the benefits of mobile UC, best practices for implementing fixed mobile convergence and mobile UC solutions as well as products that will make the execution easier.
-
Panda Adaptive Defense 360 Technologies
By: WatchGuard Technologies, Inc.
Type: White Paper
In an era of sophisticated ransomware and increasingly frequent cyberattacks, MSPs need to make sure they have comprehensive security capabilities. Access this white paper to learn how Panda Adaptive Defense 360 offers a full protection stack including endpoint protection technology, zero-trust defense, and contextualized behavior detection.
-
Malware Exploitation of Machine Identities
By: Venafi & Intel
Type: Resource
Business have seen an 8X increase in malware attacks weaponizing machine identities over the last decade. Read this infographic to explore more trends in machine identity exploitation and learn why a robust machine identity program is in order.
-
Infographic: Comparing 3 managed Kubernetes service providers
By: TechTarget ComputerWeekly.com
Type: Infographic
Kubernetes can be difficult for an enterprise to handle on its own. However, there are a variety of managed service options available today that can handle these tasks. In this infographic, we compare the three major managed Kubernetes service providers: Red Hat OpenShift, Rancher and DigitalOcean Kubernetes.
-
Ensuring the best meeting room experience
By: Logitech Inc.
Type: White Paper
As offices prepare to re-open, organizations are expanding their investments in collaboration technology to support a hybrid workforce. Download this white paper to discover what it takes to ensure the best experience for your meeting rooms.
-
Creating Equitable Hybrid Meetings: A Practical Guide
By: Logitech Inc.
Type: White Paper
With 83% of executives now expecting to support some level of hybrid or completely remote work, it has become crucial that organizations design meetings that allow everyone equal opportunity to participate in the conversation. Access this guide see how your organization can create equitable hybrid meetings.
-
Case Study: French national research centre insources with Rubrik backup
By: TechTarget ComputerWeekly.com
Type: Case Study
France's national research organisation wanted to insource IT back from Atos and built its private cloud on VMware across two locations with Rubrik appliances for backup.
-
Infographic: Windows 11 vs. Windows 10
By: TechTarget ComputerWeekly.com
Type: Infographic
The new Windows 11 was launched last year and have some features that might be worth considering. Even though support for Windows 10 won't end anytime soon, some of the new features can be an advantage depending on your needs. To help you decide if upgrading is right for you, here are some of the differences between Windows 11 and Windows 10.
-
SASE: Solving 7 Major IT Challenges
By: Superloop
Type: Case Study
Browse this case study to track a manufacturing organization’s journey from legacy SD-WAN to a SASE solution that addressed the company’s seven major IT obstacles.
-
IoT security: 5 requirements across all use cases
By: Allegro Software
Type: White Paper
With billions of IoT endpoints, how can you manage IoT security related risks? One thing to keep in mind is that regardless of the IoT application there are 5 common recurring requirements for IoT ecosystem security. Find out what they are in this white paper and learn how to bolster your IoT security.
-
Royal Holloway: Driverless vehicle security for military applications
By: TechTarget ComputerWeekly.com
Type: Research Content
Existing attacks and risk assessment frameworks within civilian autonomous vehicles (AVs) can be used to review security of military AVs deployed for logistics purposes in a desert warzone environment.
-
Optimizing your data-classification strategy
By: Novacoast
Type: Product Overview
Classifying your data is key to ensuring that it’s properly governed and secured. And as your volume of data grows, optimizing your classification strategy becomes even more important. In this overview, unlock insights that can help you improve your approach to data classification.